Researchers on Wednesday (last week) announced a major cybersecurity find—the world’s first-known instance of real-world malware that can hijack a computer’s boot process even when Secure Boot and other advanced protections are enabled and running on fully updated versions of Windows.
Researchers at security firm ESET presented a deep-dive analysis of the world’s first in-the-wild UEFI bootkit that bypasses Secure Boot on fully updated UEFI systems running fully updated versions of Windows 10 and 11.
The ultimate takeaway is that "UEFI bootkit BlackLotus" is able to install itself on up-to-date systems using the latest Windows version with secure boot enabled. Even though the vulnerability is old, it is still possible to leverage it to bypass all security measures and compromise the booting process of a system, giving the attacker control over the early phase of the system startup. It also illustrates a trend where attackers are focusing on the EFI System Partition (ESP) as opposed to firmware for their implants—sacrificing stealthiness for easier deployment—but allowing a similar level of capabilities.
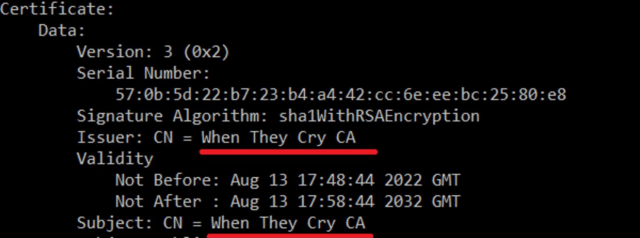
Enlarge / A self-signed certificate for the BlackLotus malware. Note the Issuer NM "When they cry CA," a reference to the Higurashi When They Cry anime series.
The handful of previously discovered bootkits in the wild—including CosmicStrand, MosaicRegressor, FinSpy, and MoonBounce (all four discovered by security firm Kaspersky) and ESPecter (like BlackLotus discovered by ESET)—provide the same benefits, but they were easily defeated by enabling Secure Boot. BlackLotus represents a major milestone in the continuing evolution of UEFI bootkits and signals the world’s continuing susceptibility to them.
BlackLotus can be removed by reinstalling Windows.
-The flaw was reported at arstechnica-
Researchers at security firm ESET presented a deep-dive analysis of the world’s first in-the-wild UEFI bootkit that bypasses Secure Boot on fully updated UEFI systems running fully updated versions of Windows 10 and 11.
The ultimate takeaway is that "UEFI bootkit BlackLotus" is able to install itself on up-to-date systems using the latest Windows version with secure boot enabled. Even though the vulnerability is old, it is still possible to leverage it to bypass all security measures and compromise the booting process of a system, giving the attacker control over the early phase of the system startup. It also illustrates a trend where attackers are focusing on the EFI System Partition (ESP) as opposed to firmware for their implants—sacrificing stealthiness for easier deployment—but allowing a similar level of capabilities.
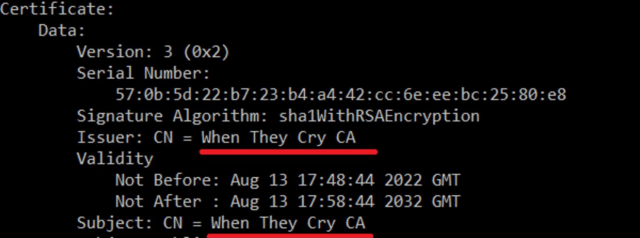
Enlarge / A self-signed certificate for the BlackLotus malware. Note the Issuer NM "When they cry CA," a reference to the Higurashi When They Cry anime series.
The handful of previously discovered bootkits in the wild—including CosmicStrand, MosaicRegressor, FinSpy, and MoonBounce (all four discovered by security firm Kaspersky) and ESPecter (like BlackLotus discovered by ESET)—provide the same benefits, but they were easily defeated by enabling Secure Boot. BlackLotus represents a major milestone in the continuing evolution of UEFI bootkits and signals the world’s continuing susceptibility to them.
BlackLotus can be removed by reinstalling Windows.
-The flaw was reported at arstechnica-
