- Downloaded
- 654.9 GB
- Uploaded
- 65.9 TB
- Ratio
- 103.06
- Seedbonus
- 5,291,337
- Upload Count
- 7 (7)
Member for 7 years


Whonix: A High-Security Method of Surfing the Internet
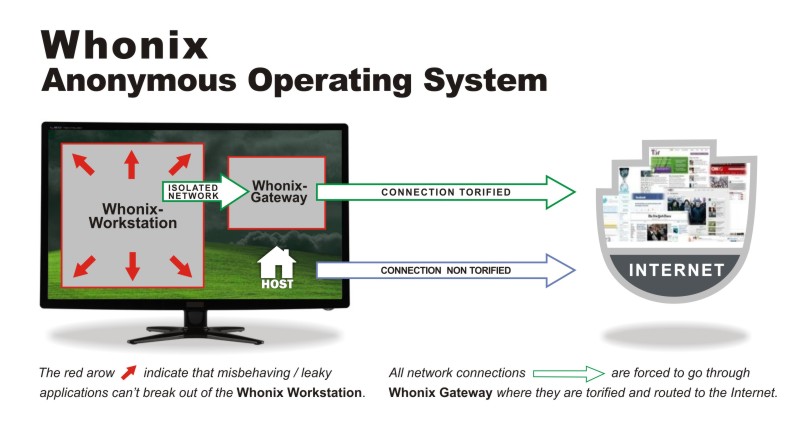
Whonix is a desktop operating system designed for advanced security and privacy. Whonix mitigates the threat of common attack vectors while maintaining usability. Online anonymity is realized via fail-safe, automatic, and desktop-wide use of the Tor network. A heavily reconfigured Debian base is run inside multiple virtual machines, providing a substantial layer of protection from malware and IP address leaks. Commonly used applications are pre-installed and safely pre-configured for immediate use. The user is not jeopardized by installing additional applications or personalizing the desktop. Whonix is under active development and is the only operating system designed to be run inside a VM and paired with Tor.
Whonix ™ consists of two VMs: the Whonix-Gateway ™ and the Whonix-Workstation ™. The former runs Tor processes and acts as a gateway, while the latter runs user applications on a completely isolated network. The Whonix ™ design affords several benefits:
- Only connections through Tor are permitted.
- Servers can be run, and applications used, anonymously over the Internet.
- DNS leaks are impossible.
- Malware with root privileges cannot discover the user's real IP address.
- Threats posed by misbehaving applications and user error are minimized.
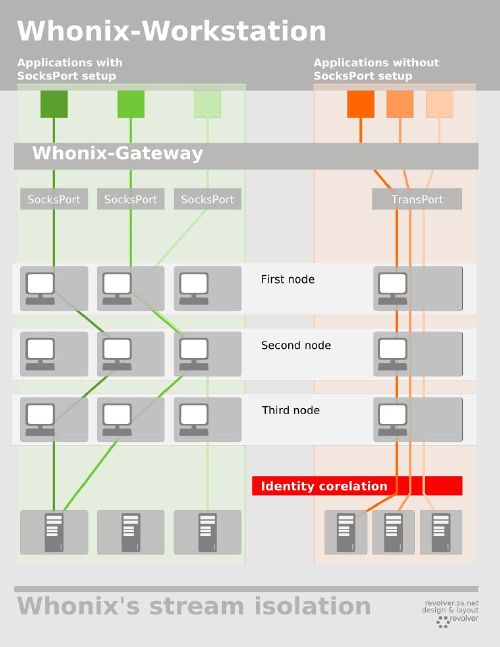
Whonix ™ provides stream isolation for many pre-installed or custom-installed applications when they are used simultaneously. For example, Tor Browser, Hexchat, Thunderbird and several other applications use a dedicated Tor SocksPort, preventing identity (pseudonym) correlation that may otherwise occur when the same Tor circuit and exit relay are used. Applications using Tor's DNS and/or Transport can be optionally disabled.

Windows XP, Vista, 7, 8, 8.1 and Windows 10
Based on Tor
Whonix utilizes Tor's free software, which provides an open and distributed relay network to defend against network surveillance.
Isolation - Leak impossibility
Connections through Tor are enforced. DNS leaks are impossible, and even malware with root privileges cannot discover the user's real IP address.
Whonix utilizes Tor's free software, which provides an open and distributed relay network to defend against network surveillance.
Isolation - Leak impossibility
Connections through Tor are enforced. DNS leaks are impossible, and even malware with root privileges cannot discover the user's real IP address.
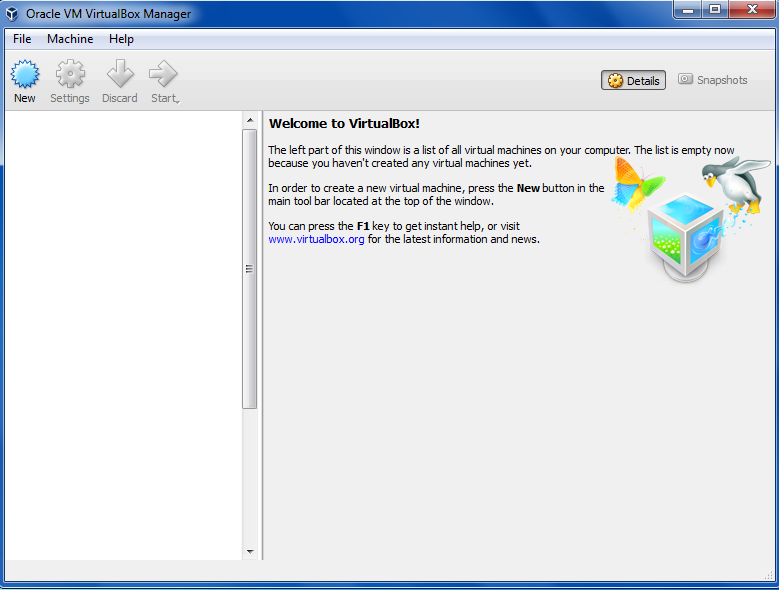
1 - Download & install VirtualBox
Thanks to @icloudsr
You must be registered for see links
Or from the official site...
2 - Download Whonix (links at the bottom)
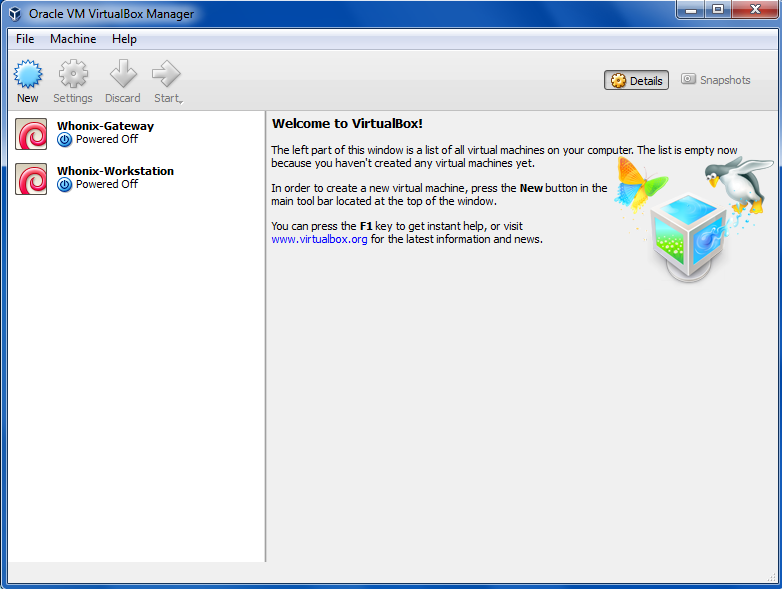
3 - Import Whonix into VirtualBox
Start VirtualBox
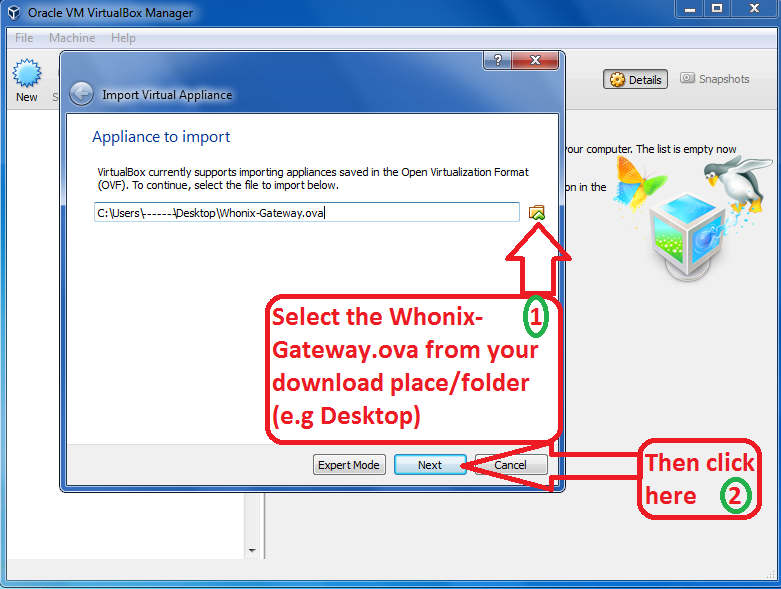
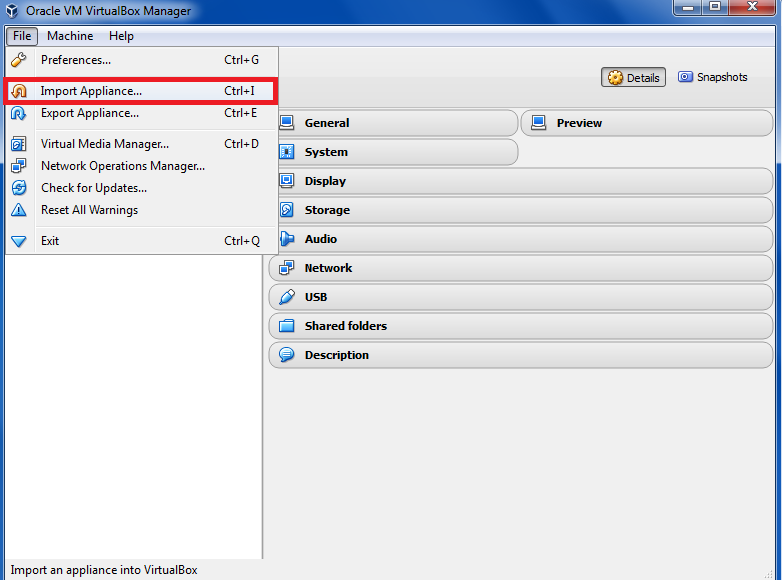
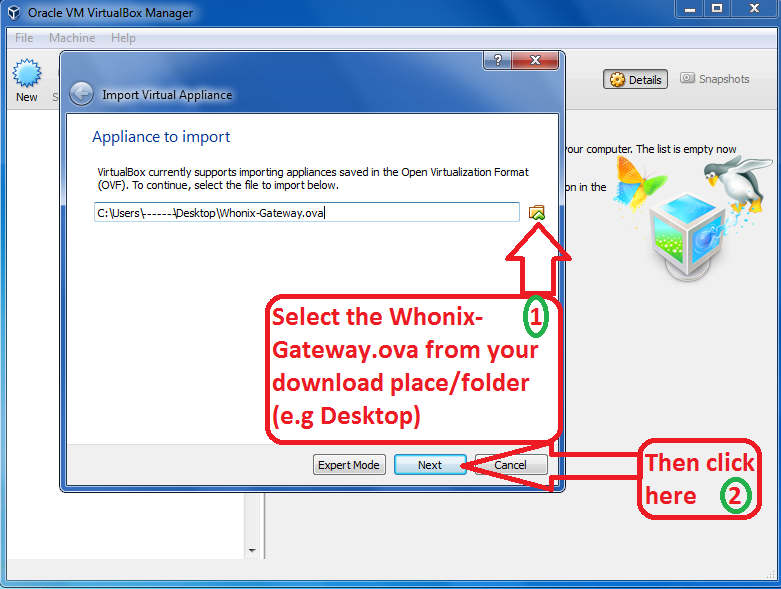
Click on File then choose Import Appliance...
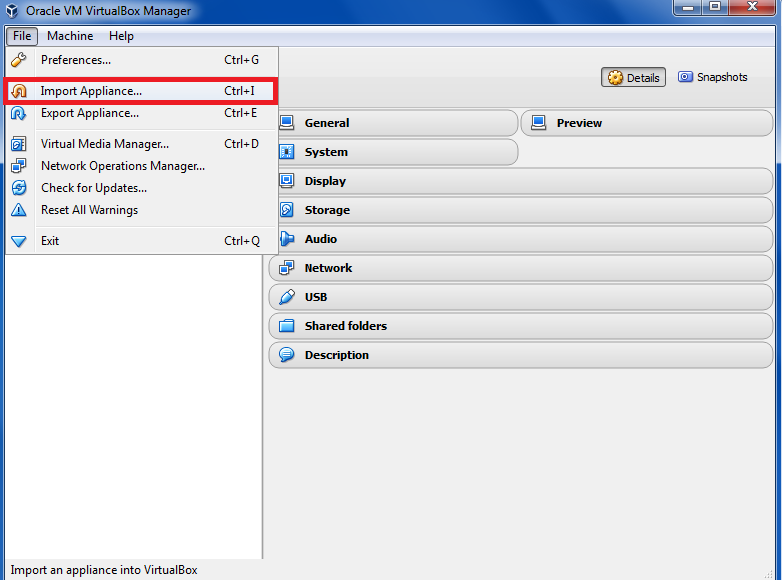
Navigate and select Whonix image and press next
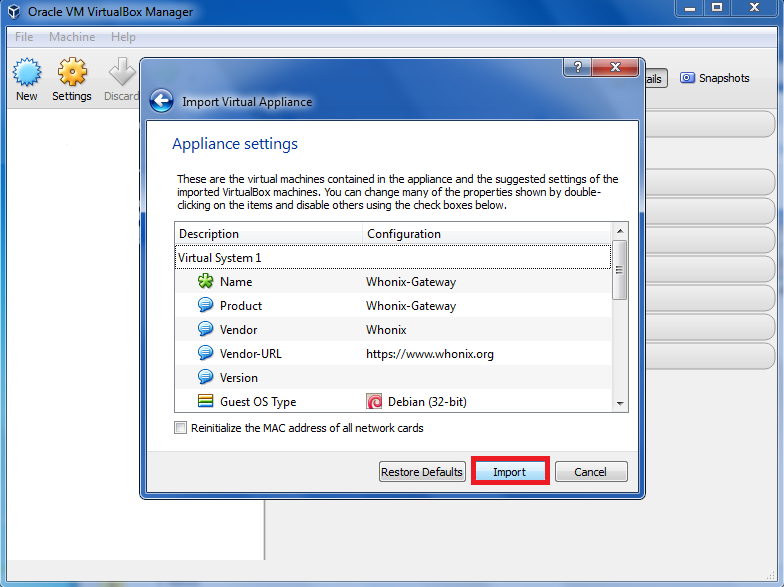
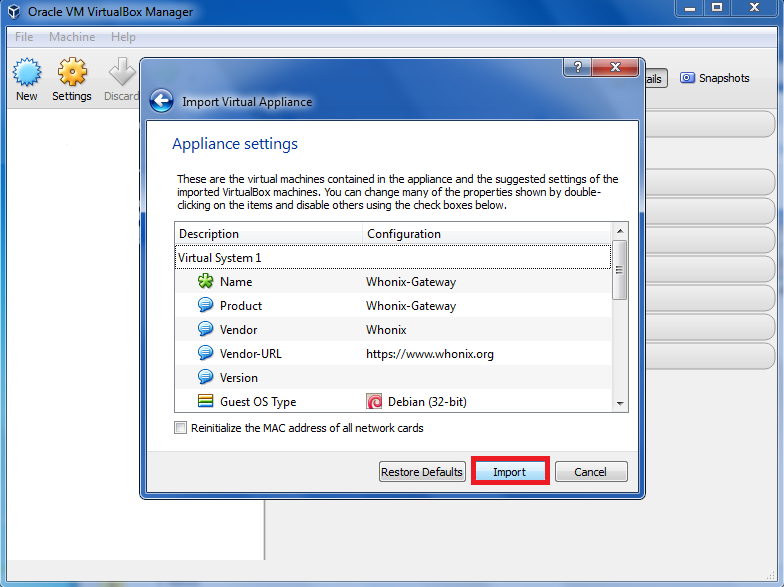
Do NOT change anything! Just click on Import
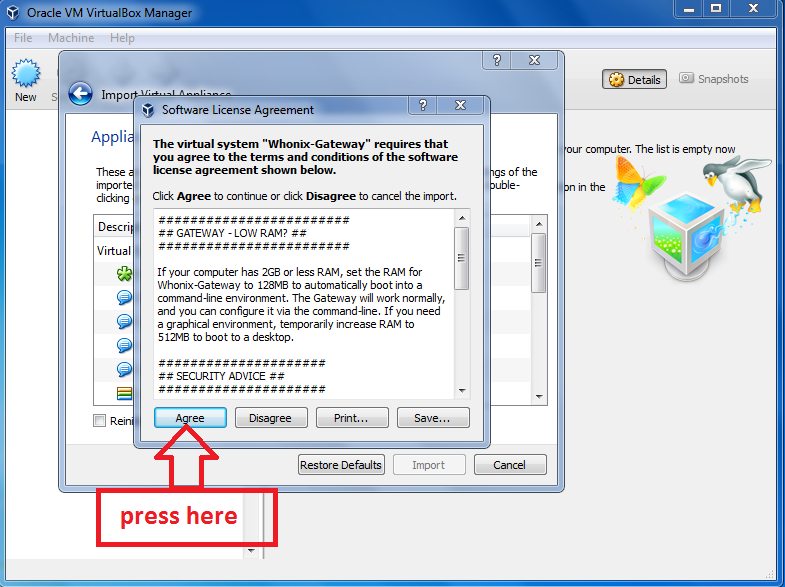
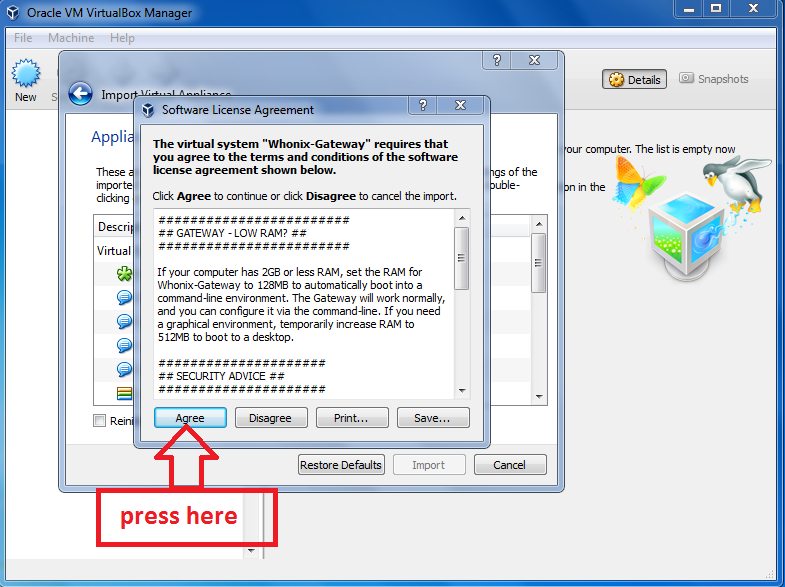
Then press Agree
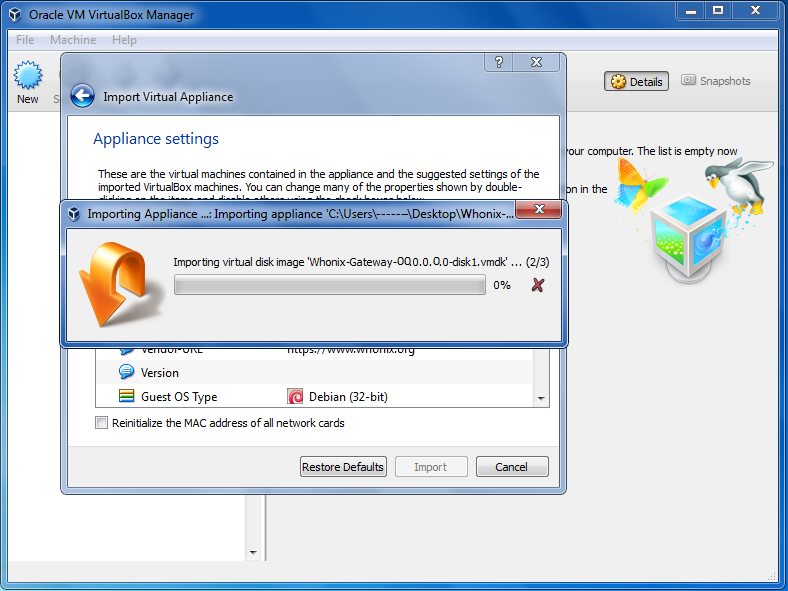
Wait until Whonix-Gateway.ova has been imported
Repeat the import step also for Whonix-Workstation.ova
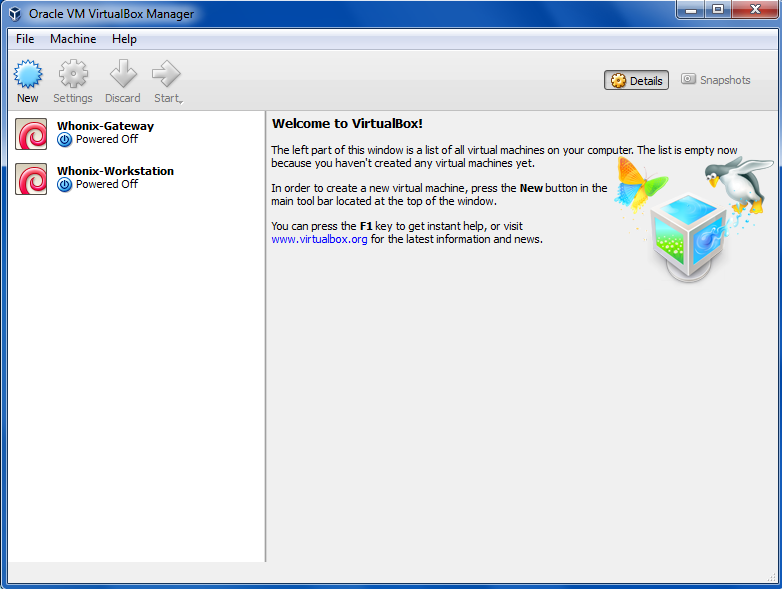
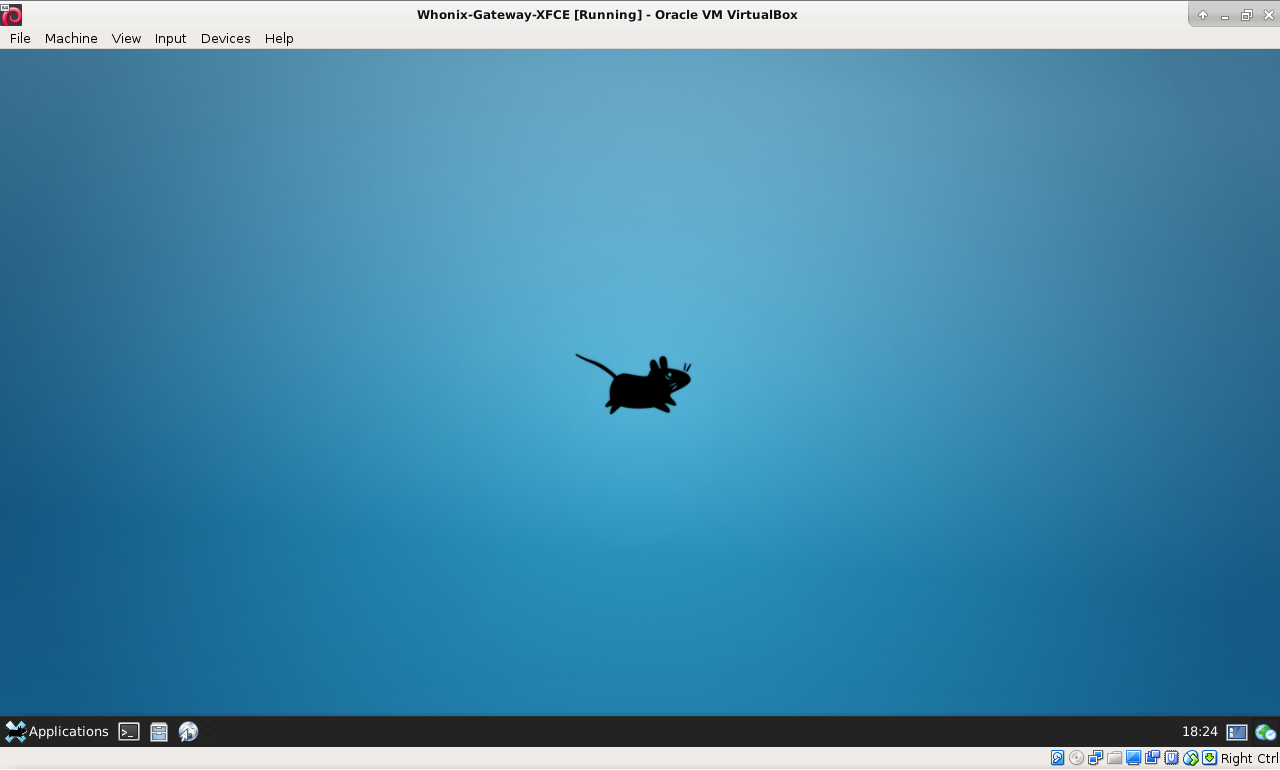
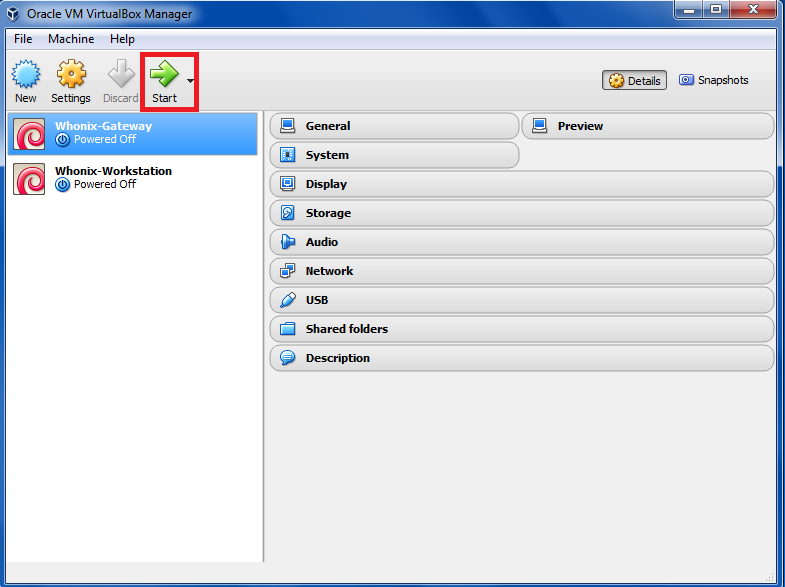
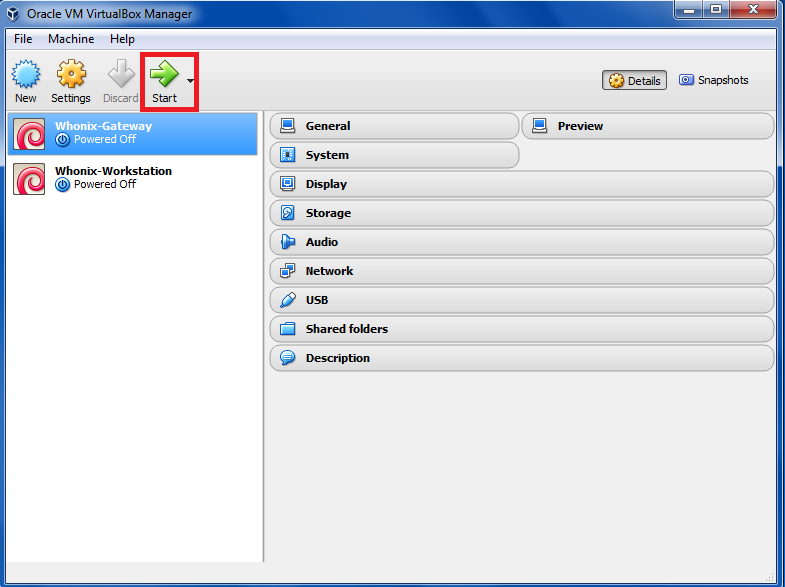
Now start FIRST Whonix-Gateway and then Whonix-Workstation
IMPORTANT - Gateway MUST be run first - and must be running in the background ALL THE TIME !!!
Then run Workstation - and "do that voodoo that you do..."
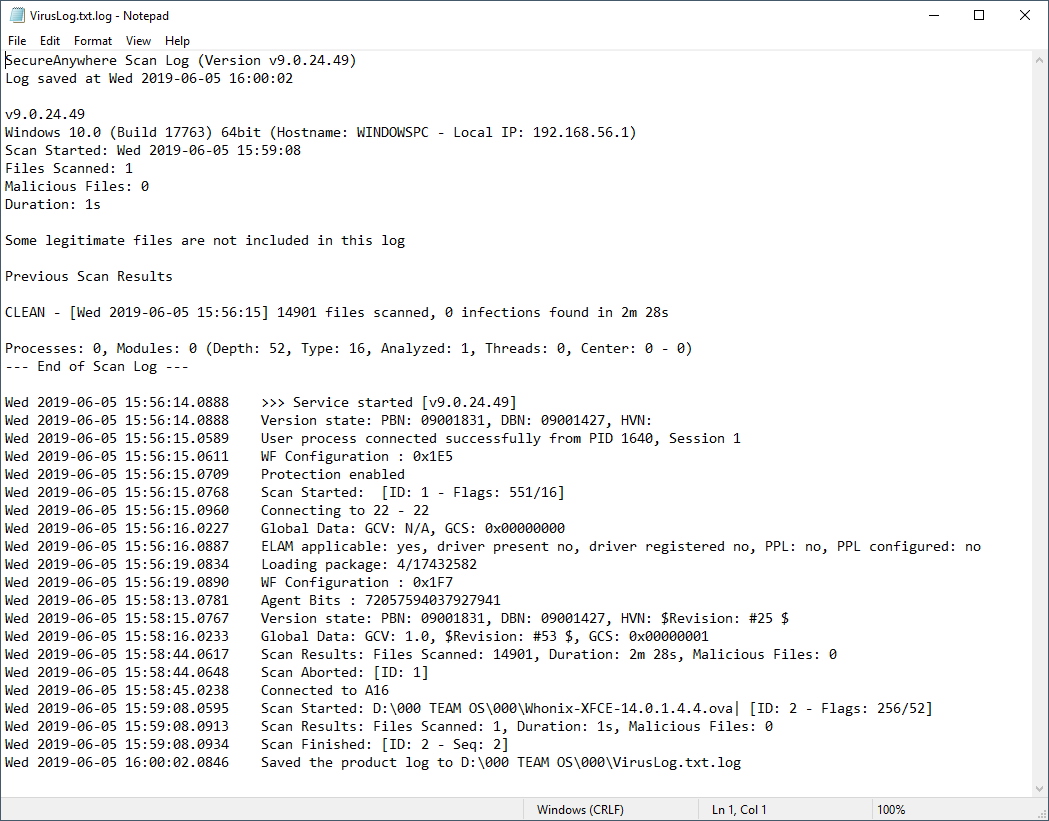
EDIT - Whonix-XFCE-14.0.1.4.4 now consist of both Gateway and Workstation in one file - you only have to import one file "Whonix-XFCE-14.0.1.4.4.ova" and both Gateway and Workstation will be imported. Sorry for the outdated instructions!
Click on File then choose Import Appliance...
Navigate and select Whonix image and press next
Do NOT change anything! Just click on Import
Then press Agree
Wait until Whonix-Gateway.ova has been imported
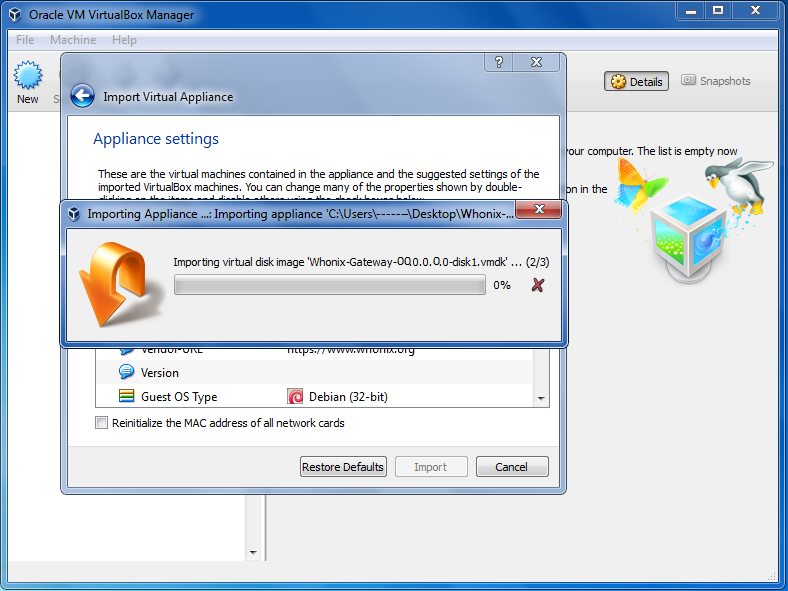
Repeat the import step also for Whonix-Workstation.ova
Now start FIRST Whonix-Gateway and then Whonix-Workstation
IMPORTANT - Gateway MUST be run first - and must be running in the background ALL THE TIME !!!
Then run Workstation - and "do that voodoo that you do..."
EDIT - Whonix-XFCE-14.0.1.4.4 now consist of both Gateway and Workstation in one file - you only have to import one file "Whonix-XFCE-14.0.1.4.4.ova" and both Gateway and Workstation will be imported. Sorry for the outdated instructions!


MEGA.NZ
You must be registered for see links
MEDIAFIRE
You must be registered for see links
DOUPLOADS
You must be registered for see links
ZIPPYSHARE(4 files)
You must be registered for see links
You must be registered for see links
You must be registered for see links
You must be registered for see links
@icloudsr - for posting VIrtualBox thread. Thanks, m8!
@Iceman96 - for reminding me of the importance of security with Kali
@00Proteus00 - for creating beautiful Virtual Images - and inspiring this thread
@Astro and @TheMacGyver - Just for being a Linux lovers and enthusiasts


Last edited: